If you run an online business then you have probably heard of a content delivery network, or CDN for short. A CDN speeds up your site immensely by loading the contents of your website from a network of servers, rather than just one server.
The biggest CDN provider is Cloudflare. I put one of my sites on Cloudflare several months ago after joining the Ezoic ad network.
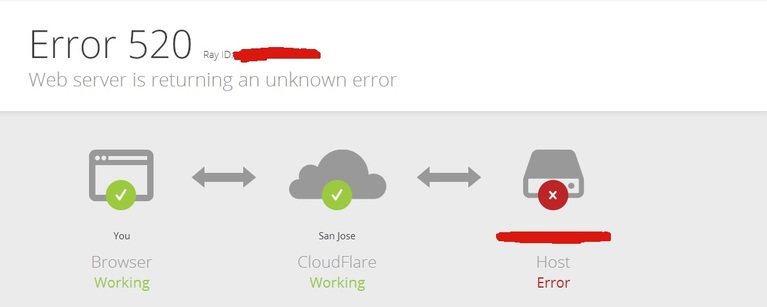
Everything was fine and dandy for awhile until a couple of months ago when I started getting Cloudflare 520 and 522 error messages that look like this:
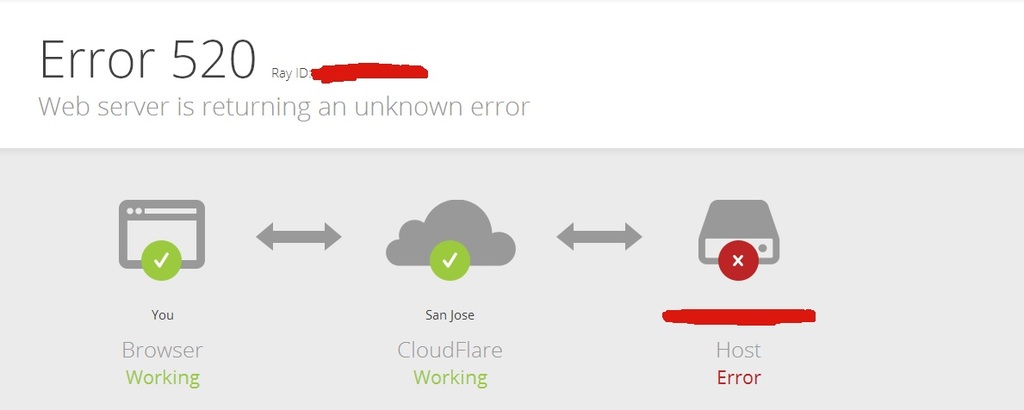
The weird thing is that my site was fine for the most part. I only got this message when I tried to log in or was in the WordPress dashboard.
So didn’t think anything of it as it wasn’t that bad initially. Then I finally got around to asking my web host about it when it happened more often.
So my host checked the logs and here is what they said:
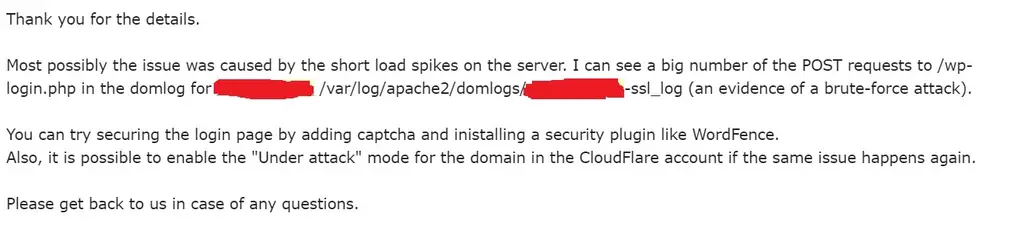
There it was. The answer. I was getting the Cloudflare 520/522 error when trying to login because my website was the victim of a brute force attack. And it happens more and more often because my website was getting bigger.
After that I immediately took actions to remedy it.
Actions I Took to Solve the Cloudflare 520/522 Errors on Login Page
1. Installed Wordfence
Yes, I am extremely stupid for not having Wordfence on it in the first place but I thought the my installed login security plugin (Loginizer Security) was good enough. So I installed Wordfence and configured reCaptcha for the login page.
2. Tweaked Loginizer Settings
I found out the default Loginizer settings were a little too generous. Here are the things I changed in Loginizer Security:
- Lowered Max Retries to 3
- Increased Lockout Time 360 minutes
- Decreased Max Lockouts to 2
3. Change Your WordPress Login URL
I got this tip from GeekFlare.
I downloaded the plugin WPS Hide Login and changed my login url. Once you activate the plugin, the default login is still pretty obvious (yoursitename.com/login/) so be sure to change it to something else if you are using the plugin.
Use Cloadflare’s Under Attack Mode For WordPress Login Pages
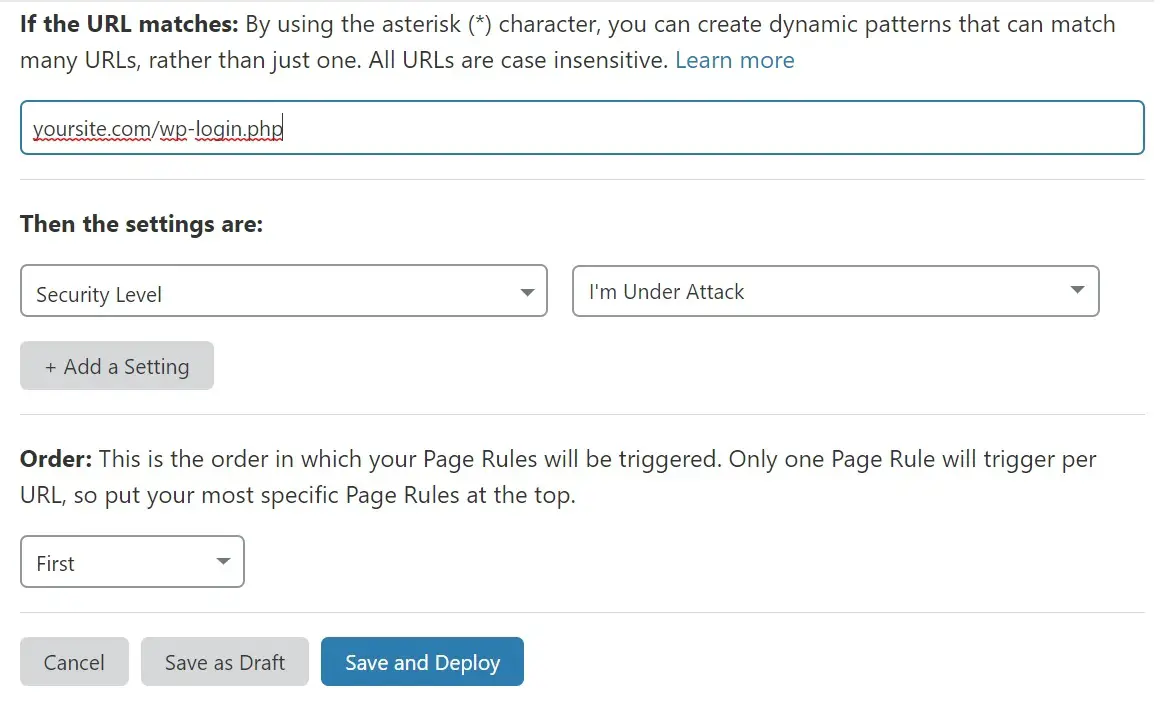
In addition to the three steps above, I turned on’ Cloudflare’s Under Attack mode for my login pages (yoursite.com/wp-admin/ and yoursite.com/wp-login.php). When you turn on the Under Attack mode, this is what you see for the page:
Cloudflare gives you the option of turning on the mode on specific pages. I turned it on for the login pages. You can do that with Cloudflare’s Page Rules. Once you are on the Page Rules page, you enter your the login urls of your site and choose Security Level—>I’m Under Attack. See example below:
How To Know If There’s A Brute Force Attack On Your WordPress Site
I am not a techie so without my web host informing me, there was no way to know that the 520/522 errors were the result of my site being attacked.
My web host provider checked the domain logs (domlog) and noticed a big number of POST requests for /wp-login.php. That was what they told me. So if you are noticing this Cloudflare error, I would e-mail your web host to check the logs for this. I am not a server guy so I wouldn’t know what to look for. Knownhost has a pretty extensive article on how to isolate your logs to look for abuse.
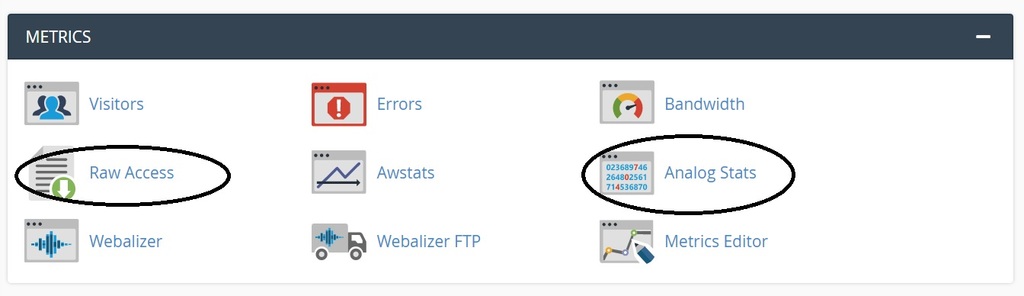
To get access and raw logs for your site via Cpanel, you just need to log into your Cpanel and either click Raw Access or Analog Stats.
I hope this article gave you a clue as to what might be going on with your site if you get a Cloudflare 520/522 error when trying to log into your WordPress site. I had the toughest time trying to search for the solution when it was happening to me so I hope this provides you with some insight. Again, your situation might be different than mine and you might not be getting attacked—but I hope this article provides you with a good starting point to investigate your issue.
Additionally, if you are concerned about your privacy and online security, I recommend using a VPN. We compiled a list of 8 free VPNS (with USA IP addresses) for you to choose from.


2 Responses
Hi, thanks for telling us your experience. I just signed up for Ezoic, and I already have wordfence. But I’m getting the message that it is not compatible with wordfence. Did you get that problem?
Hey Ivy. I’ve heard people have that problem sometimes and I think it has to do with Wordfence blacklisting a lot of IPs. Try setting your Wordfence in learning mode or try to whitelist your Ezoic IP perhaps?