If you have a virtual assistant or a virtual team, you will want to share certain accounts with them in order for them to accomplish projects. But upon doing so, you run into the problem of having to worry about giving out your passwords.
That’s what I used to do. I used to give my virtual assistants and contractors my login credentials and then change them after they are no longer using it. This got really tiresome to keep track of after awhile because you don’t know who has what passswords.
Then I discovered the password management tool LastPass.
Lastpass is a password management tool that lets you share your login information with others without sharing your username or password. Here’s how it works.
How Does LastPass Work and How to Use It
For a little tutorial of how LastPass works, I did a little video tutorial on the Youtube channel that you can watch below if you want to find out how to use it.
Essentially, how it works is that you make an account and store all your login information there.
Then once you store the login information in your LastPass dashboard, you can invite someone via e-mail to share that login information with.
Once they accept the invitation, they are invited to sign up and download the browser extension or app (if on phone). Once done, they will be able to log in to any website you allow them to.
So once they are at the login screen, the credentials will autofill with *** and they will be able to log in but unable to see your credentials. Here is what it will look like on their end.
And if you somehow need to change your password, there is nothing that needs to be done on their end. LastPass will automatically update the credentials.
I use this quite often now and it has saved me immense time and headache. I this for my virtual assistants, writers, and marketers. They can log into my web hosting dashboard, Grammarly Premium, marketing services, etc.
And if you no longer want to share the login credentials with that person, you just remove their e-mail address from the said service/website in the LastPass dashboard. Easy. No need to change your password or anything.
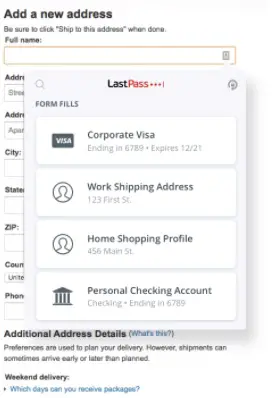
In addition to storing your passwords, you can also store your credit card and bank information there. So if your team needs to charge something on your card or to your bank, they can do so without knowing your bank information or credit card numbers.
If you share your credit card or bank information with your staff, they will see something like this:
How Much Does LastPass Cost?
To the people that you are sharing your login info with, it will cost them nothing. And for you, there is a free option. However, the free option is limited in that you can only share each website/account with one person.
So for instance, if you want to share the login information of your website, you can only share it with one person at a time. So both your virtual assistant and web designer cannot have access at the same time.
That’s why I like the Premium option. The Premium option costs only $3/mo and allows you to share your credentials with as many people as you want (one-to-many sharing).
In addition to one-to-many sharing, Premium also offers a plethora of other features including:
- Emergency Access – Grant someone emergency access to your account in case of emergency
- 1 gb of encrypted file storage
- Dark web monitoring – LastPass watches all your account to see if they have been compromised in the dark web
- Advance multi-factor authentication – Yubikey and fingerprint authentication available for an extra layer of security for those you are sharing passwords with
Is LastPass Secure and Safe?
So how secure is LastPass? It’s pretty dang secure. First, they use zero-knowledge encryption—meaning LastPass will never have knowledge of any of your encrypted information.
Whatever you store in the LastPass vault is for your eyes and your eyes only. No one at LastPass or anyone that hacks LastPass knows what’s inside your password vault.
Furthermore, the information your store is encrypted with AES-256 bit encryption with PBKDF2 SHA-256 and salted hashes to ensure complete security in the cloud.
It also is locally encrypted at the device level so that your passwords are never at risk if the person you share the password with is hacked. They also offer multifactor authentication for extra measure.
How Good is AES-256 and PBKDF2 SHA-256 Encryption?
Well according to enterprise computing security company ATP, AES has a key length of 256 bits and is virtually unbreakable by brute force using current computing power. With 256 bits (AES), there are 1.1*10^77 possible combinations. That’s a lot of possible combinations.
And SHA-256 is one of the most secure hashing functions on the market. The United States government actually requires all of its agencies to protect sensitive information with SHA-256 encryption.
Has LastPass Ever Been Hacked?
LastPass has been in the business for over 10 years and has never had its users encrypted information stolen. However, they did experience a security breach in 2015 when LastPass account e-mail addresses were compromised. But passwords stored with LastPass were safe and not compromised.
Because LastPass uses zero knowledge encryption, someone would have to hack your account individually in order to obtain passwords in your vault. Your password are not available on the LastPass system.
In that regard, they have done much better than many other companies who have much more of our data, including the government.
Conclusion
LastPass has been a lifesaver and saved me a bunch of time. If you want to increase the productivity of your remote team, include LastPass as one of your tools. It has also saved me tons of money as I do not need to get individual accounts for every member on the team, especially for members that only use the account once in a blue moon.